Azure Network Security
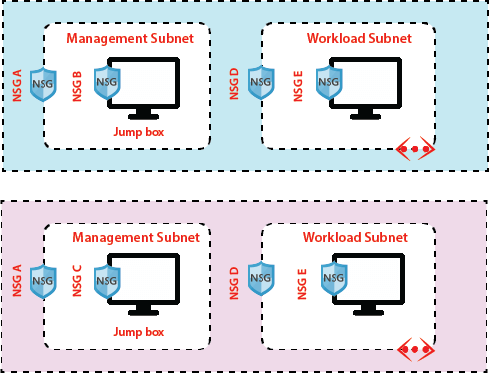
A network security group consists of security rules that allow or deny inbound/Outbound network traffic to or from different types of Azure resources that we will host in our Azure virtual network. And we can apply the network security group at different levels. For example:
Security rule properties:
Name: The name of the network should be unique within the network security group.
Priority: Security rules are processed in priority order with a lower number has the highest priority.
Source or Destination: (The IP address, CIDR (Classless inter-domain routing) block, service tag, or application security group) The ability to specify multiple individual IP addresses and ranges in a rule is referred to as augmented security rules.
Protocol: TCP, UDP, etc.
Port range: we can specify an individual or range of ports
Action: Allow or Deny
Service Tags
Service tag represents a group of IP address prefixes to help minimize complexity for security rule creation. We cannot create our service tag, nor specify which Ip address is included within a tag. Microsoft manages the address prefixes encompassed by the service tag, and automatically updates the service tag as an address change.
Earlier, if we want to allow communication to Azure service from our virtual machine, we need to configure IoT of outbound rules because Microsoft is providing list of IP addresses for each service you need to configure those list of IP addresses in our NSG rule to allow outbound connection from our virtual machine to that particular service and also in case if Microsoft is changing the addresses you need to change your rules.
Using service tags will simplify your NSG rules a lot, for example:
Storage: This tag denotes the IP address space for the Azure Storage service. If you specify Storage for the value, traffic is allowed or denied to storage.
SQL: This tag denotes the address prefixes of the Azure SQL Database, Azure Database for MySQL, Azure Database for PostgreSQL, and Azure SQL Data Warehouse services.
Azure CosmosDB: This tag denotes the address prefixes of the Azure Cosmos Database services.
AzureKeyVault: This tag denotes the address prefixes of the Azure KeyVault service. If you specify AzureKeyVault for the value, traffic is allowed or denied to AzureKeyVault.
EventHub: This tag denotes the address prefixes of the Azure EventHub service. If you specify EventHub for the value, traffic is allowed or denied to EventHub.
Default Rules
Some default rules are created by default when we create NSG. There are two types of default rules.
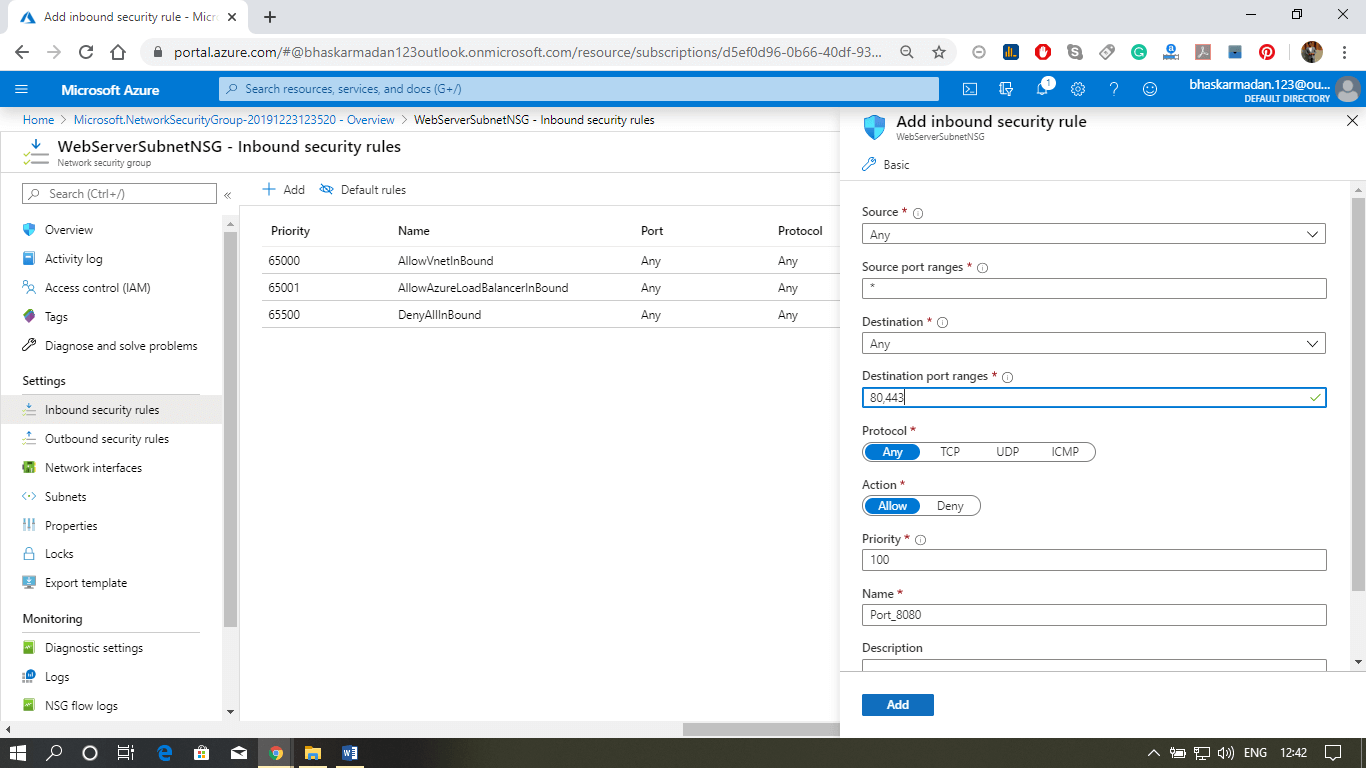
Inbound Security rules
- AllowVNetInbound: Traffic is allowed from any resources within the VNet
- AllowAzureLoadBalancerInbound: Any traffic originating from Azure load-balancer to any of the virtual machines within the network is permitted.
- DenyAllInbound: By default, virtual machines in the virtual network can communicate with each other, and also Azure load balancer can communicate with virtual machines within the virtual network.
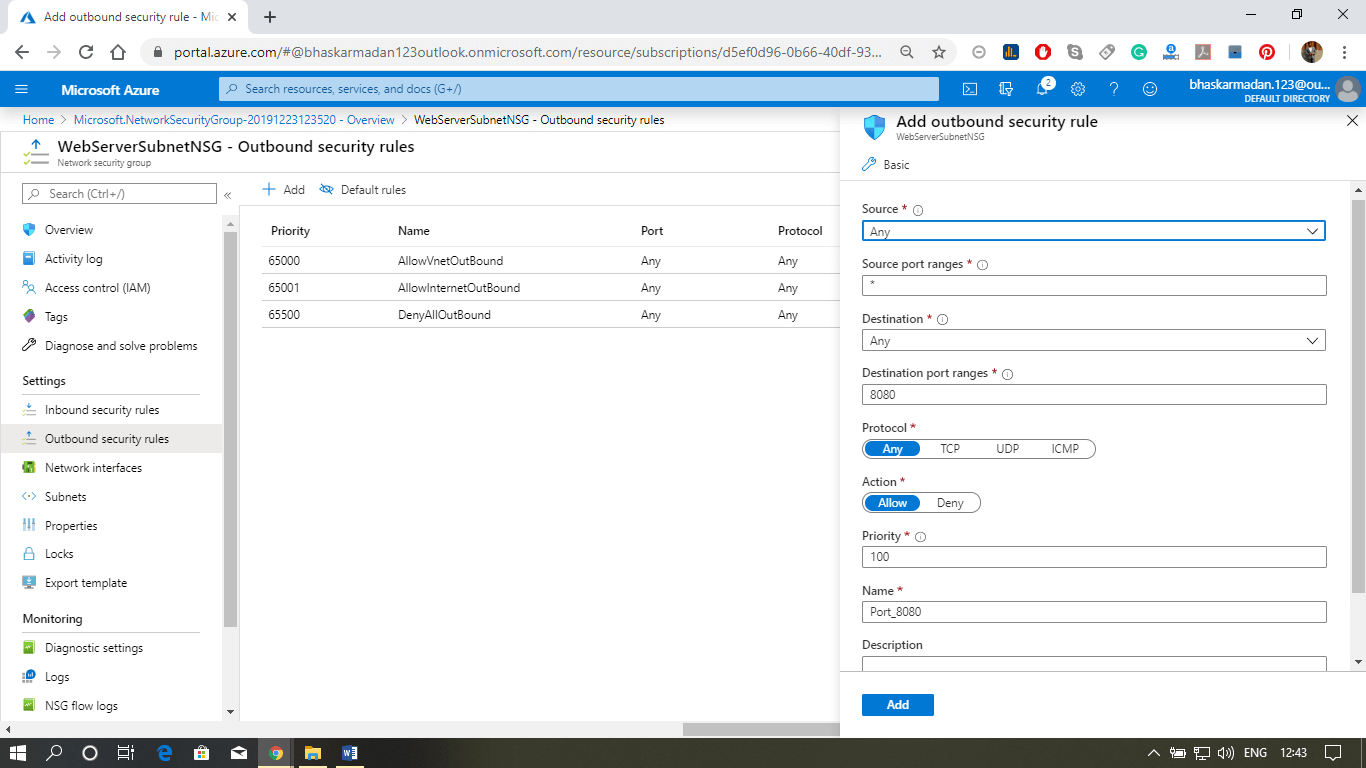
Outbound Security rules
- AllowVNetOutBound: Traffic is allowed through any resources within the VNet
- AllowInternetOutBound: Traffic originating from any resources in the VNet to the Internet is allowed.
- DenyAllOutBound: By default, virtual machines in a virtual network can communicate with each other, and also Azure load balancer can interact with the virtual machine within the virtual network.
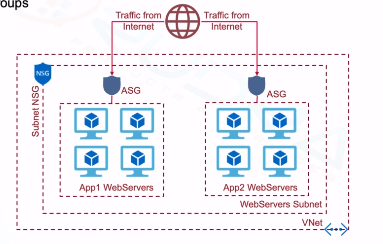
Application Security Groups
Application security groups enable you to configure network security as a natural extension of an application’s structure, allowing you to group virtual machines and define network security policies based on those groups. For example –
Configuring an NSG at Subnet and VM level
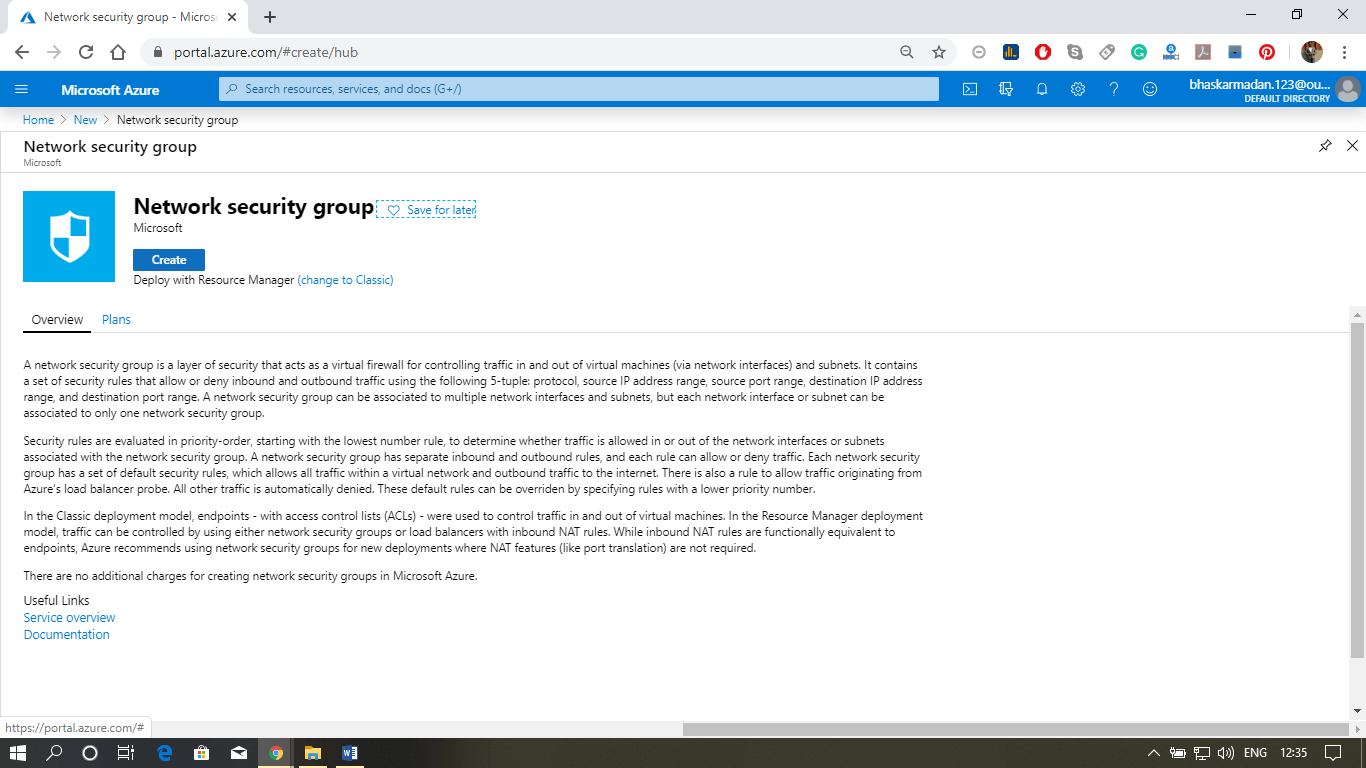
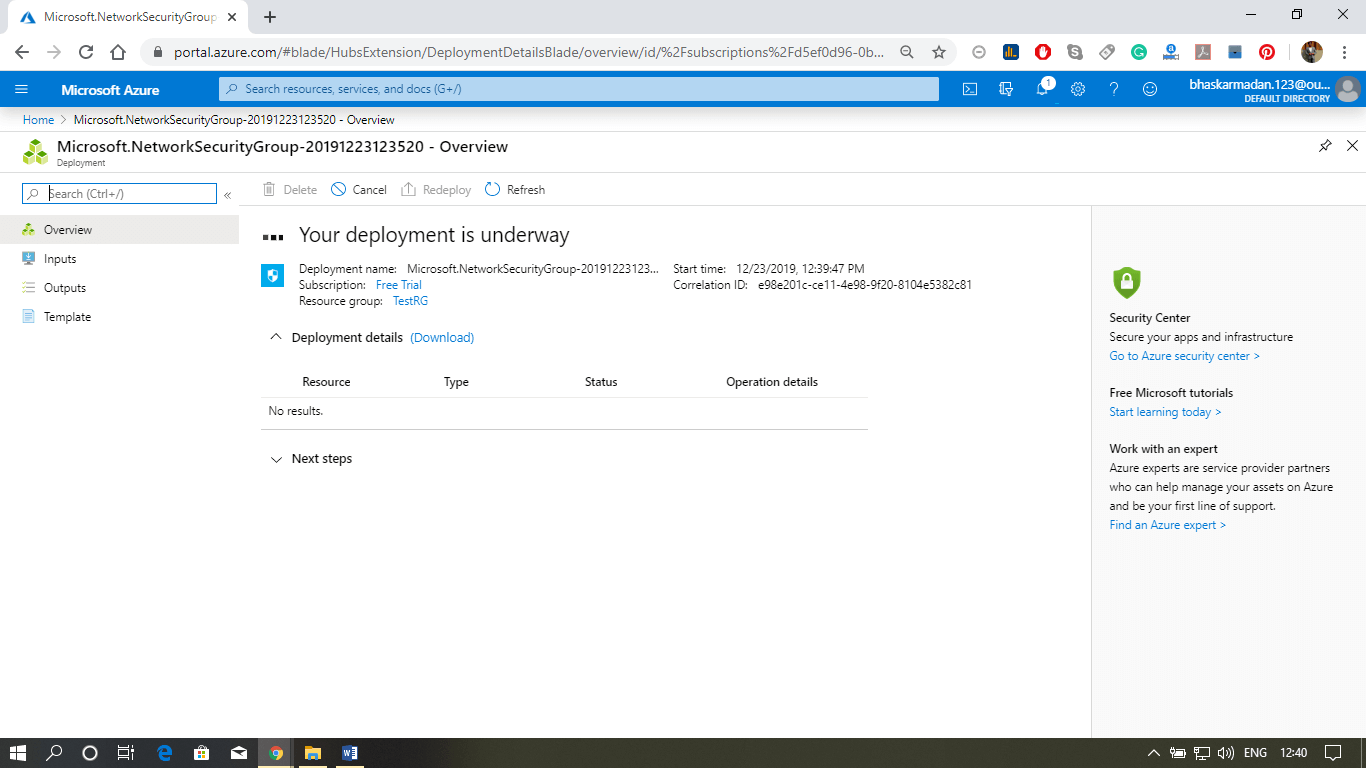
Step 1: Click on create a resource button and type-in Network Security Group. Then select Network Security Group, and click on create button.
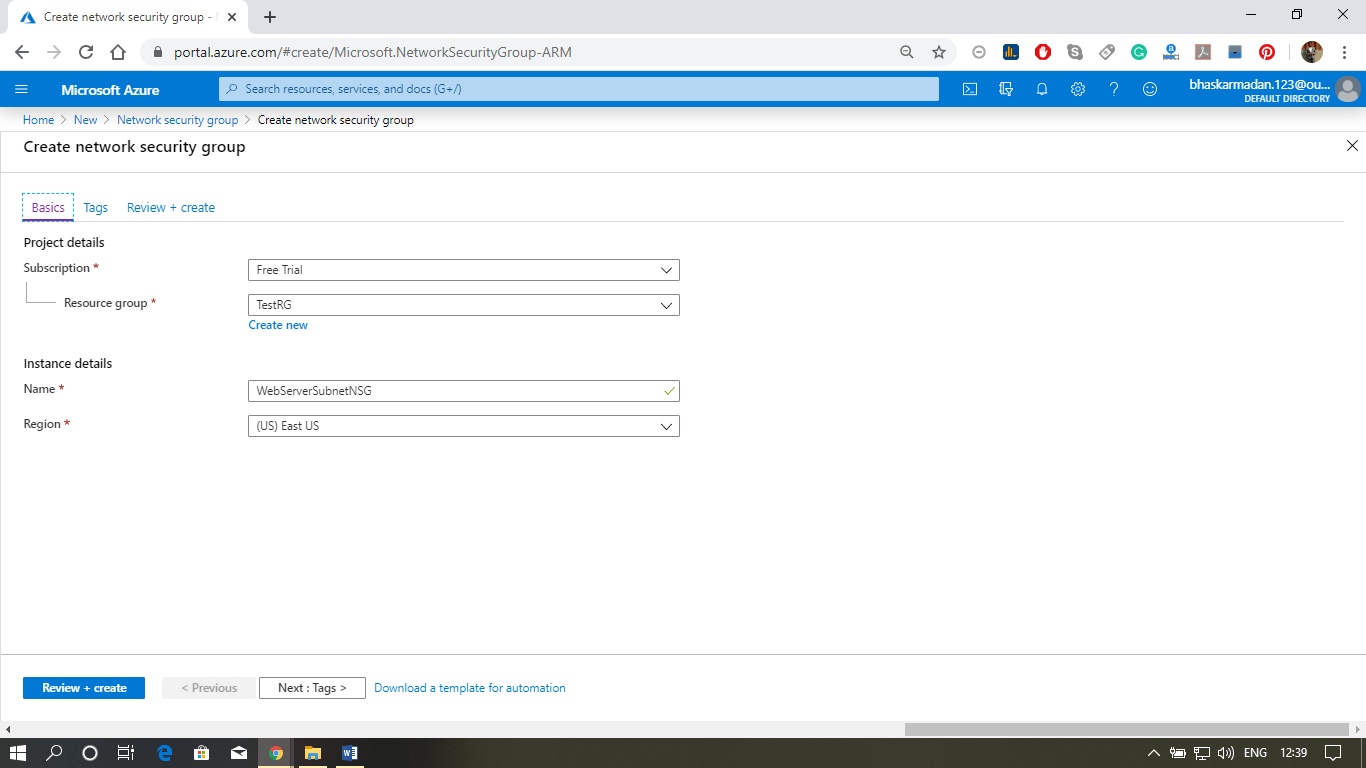
Step 2: Now, you are on the Network Security Group creation page. Select the resource group, fill the name, select the region, and click on review+create.
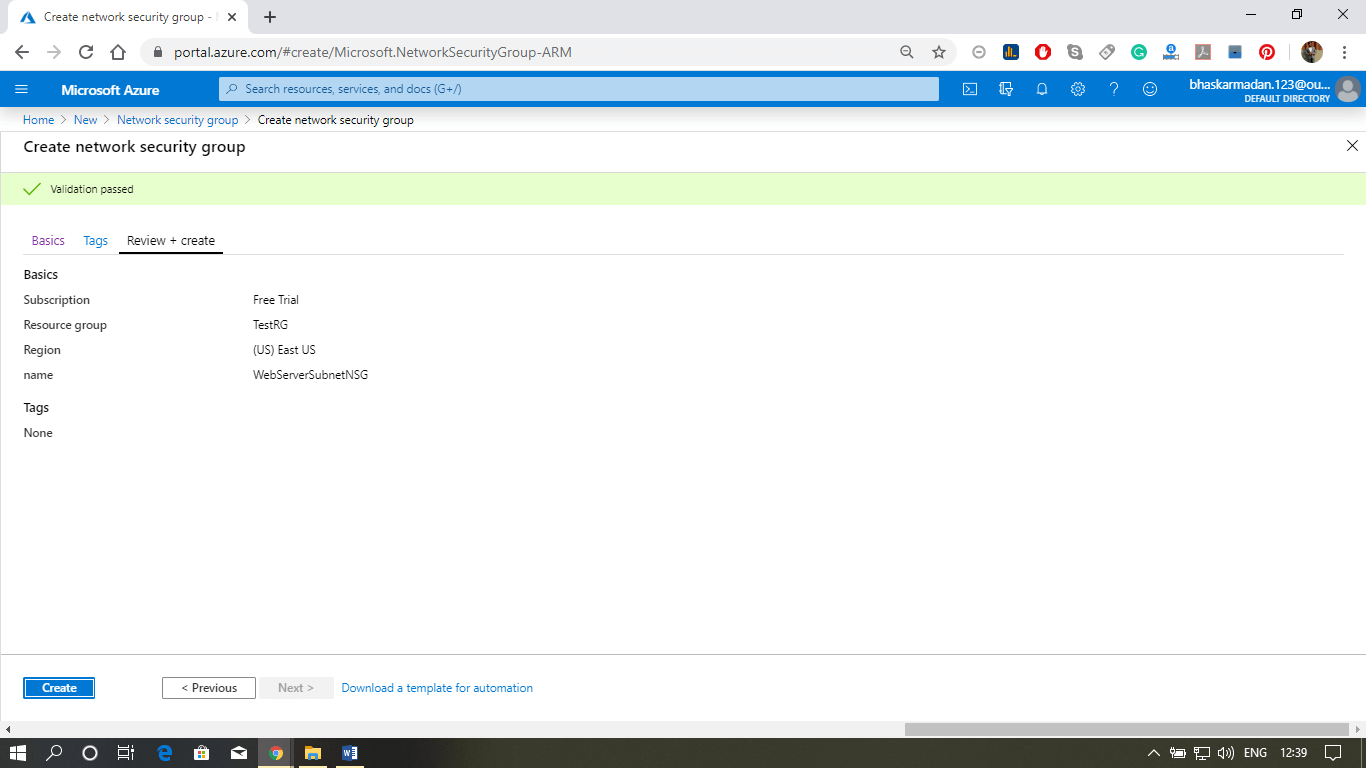
Step 3: Your NSG is created, now we will associate this NSG with the subnet.
Step 4: Click on the subnet, then click on add Associate. Select the virtual network and subnet with which you want to associate this NSG.
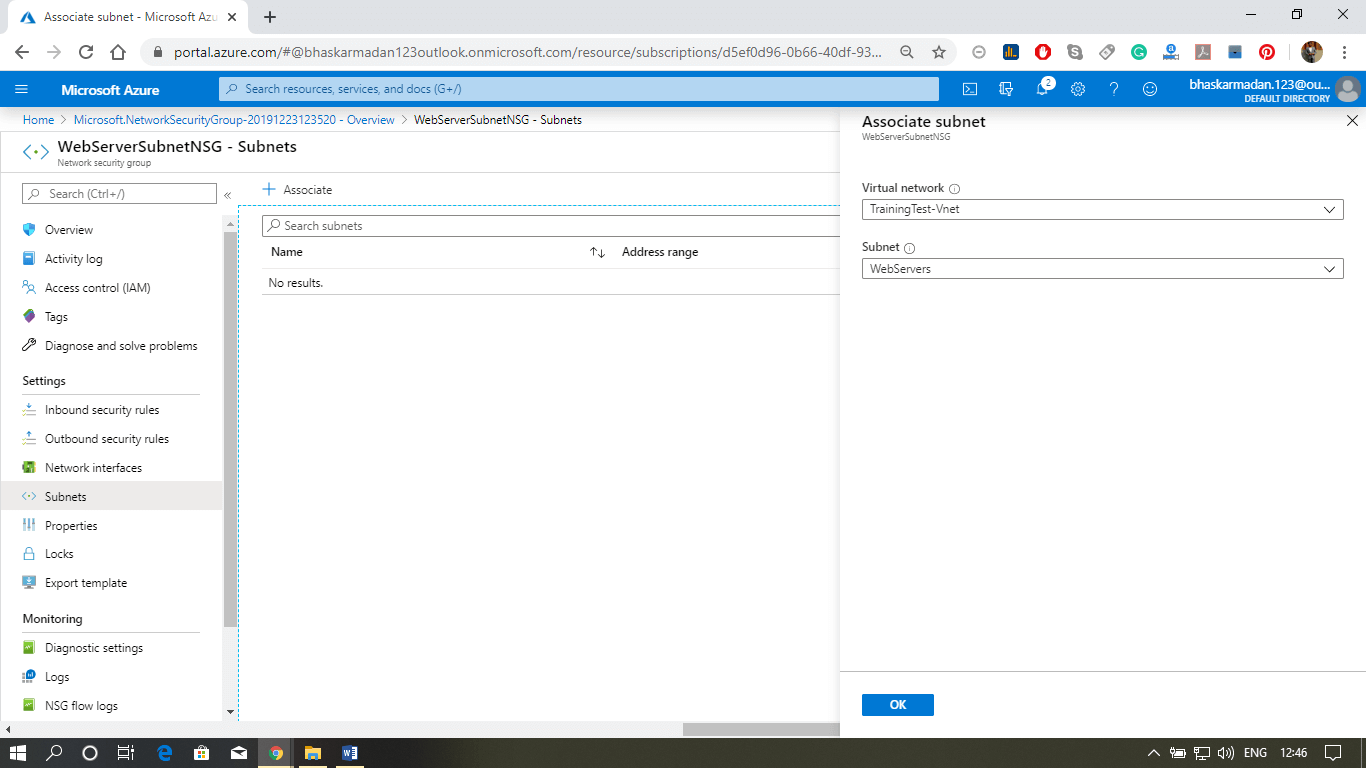
Step 5: Finally, click on the ok button. Your NSG is now associated with the subnet.