Vigenere Cipher
Introduction
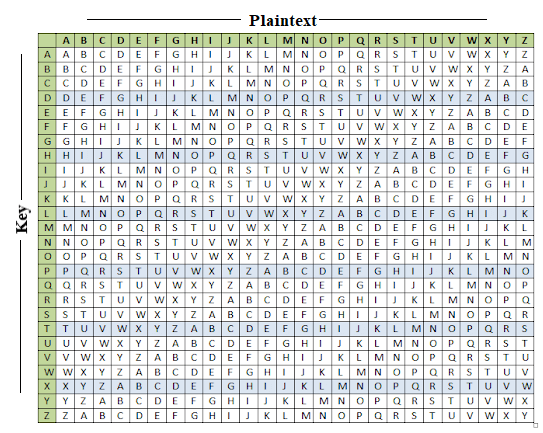
The vigenere cipher is an algorithm that is used to encrypting and decrypting the text. The vigenere cipher is an algorithm of encrypting an alphabetic text that uses a series of interwoven caesar ciphers. It is based on a keyword’s letters. It is an example of a polyalphabetic substitution cipher. This algorithm is easy to understand and implement. This algorithm was first described in 1553 by Giovan Battista Bellaso. It uses a Vigenere table or Vigenere square for encryption and decryption of the text. The vigenere table is also called the tabula recta.
Two methods perform the vigenere cipher.
Method 1
When the vigenere table is given, the encryption and decryption are done using the vigenere table (26 * 26 matrix) in this method.
Example: The plaintext is “TUTORASPIRE”, and the key is “BEST”.
To generate a new key, the given key is repeated in a circular manner, as long as the length of the plain text does not equal to the new key.
Encryption
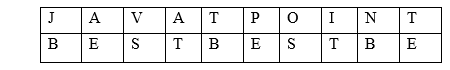
The first letter of the plaintext is combined with the first letter of the key. The column of plain text “J” and row of key “B” intersects the alphabet of “K” in the vigenere table, so the first letter of ciphertext is “K”.
Similarly, the second letter of the plaintext is combined with the second letter of the key. The column of plain text “A” and row of key “E” intersects the alphabet of “E” in the vigenere table, so the second letter of ciphertext is “E”.
This process continues continuously until the plaintext is finished.
Ciphertext = KENTUTGBOX
Decryption
Decryption is done by the row of keys in the vigenere table. First, select the row of the key letter, find the ciphertext letter’s position in that row, and then select the column label of the corresponding ciphertext as the plaintext.
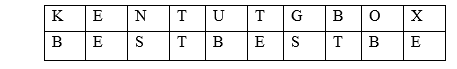
For example, in the row of the key is “B” and the ciphertext is “K” and this ciphertext letter appears in the column “J”, that means the first plaintext letter is “J”.
Next, in the row of the key is “E” and the ciphertext is “E” and this ciphertext letter appears in the column “A”, that means the second plaintext letter is “A”.
This process continues continuously until the ciphertext is finished.
Plaintext = TutorAspire
Method 2
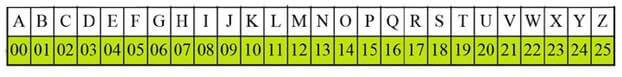
When the vigenere table is not given, the encryption and decryption are done by Vigenar algebraically formula in this method (convert the letters (A-Z) into the numbers (0-25)).
Formula of encryption is,
Formula of decryption is,
If any case (Di) value becomes negative (-ve), in this case, we will add 26 in the negative value.
Where,
E denotes the encryption.
D denotes the decryption.
P denotes the plaintext.
K denotes the key.
Note: “i” denotes the offset of the ith number of the letters, as shown in the table below.
Example: The plaintext is “TUTORASPIRE”, and the key is “BEST”.
Encryption: Ei = (Pi + Ki) mod 26
| Plaintext | J | A | V | A | T | P | O | I | N | T |
| Plaintext value (P) | 09 | 00 | 21 | 00 | 19 | 15 | 14 | 08 | 13 | 19 |
| Key | B | E | S | T | B | E | S | T | B | E |
| Key value (K) | 01 | 04 | 18 | 19 | 01 | 04 | 18 | 19 | 01 | 04 |
| Ciphertext value (E) | 10 | 04 | 13 | 19 | 20 | 19 | 06 | 01 | 14 | 23 |
| Ciphertext | K | E | N | T | U | T | G | B | O | X |
Decryption: Di = (Ei – Ki) mod 26
If any case (Di) value becomes negative (-ve), in this case, we will add 26 in the negative value. Like, the third letter of the ciphertext;
N = 13 and S = 18
Di = (Ei – Ki) mod 26
Di = (13 – 18) mod 26
Di = -5 mod 26
Di = (-5 + 26) mod 26
Di = 21
| Ciphertext | K | E | N | T | U | T | G | B | O | X |
| Ciphertext value (E) | 10 | 04 | 13 | 19 | 20 | 19 | 06 | 01 | 14 | 23 |
| Key | B | E | S | T | B | E | S | T | B | E |
| Key value (K) | 01 | 04 | 18 | 19 | 01 | 04 | 18 | 19 | 01 | 04 |
| Plaintext value (P) | 09 | 00 | 21 | 00 | 19 | 15 | 14 | 08 | 13 | 19 |
| Plaintext | J | A | V | A | T | P | O | I | N | T |
Program:
C language
Output:
I AM INDIAN Encrypted: SDERFGTUJ Decrypted: IAMINDIAN